12 Tips to Protect Your PEX Account from Risks & Attacks

Contrary to popular belief, online criminals don’t only look for easy targets. If the target is banking or other financial services, they’ll work harder to penetrate defenses to get to your account. Here are 12 tips to protect your account, including some that let you take advantage of the special security tools that PEX offers.
1. First Things First, Use Strong Passwords
No surprise that this tops the list of so many lists of security tips. Passwords are still your first and most important line of defense against criminals. And everything you’ve heard about creating passwords applies to PEX, too:
- Make them 12 – 16 characters long
- Mix it up with a combination of uppercase letters, lowercase letters, numbers, and special characters
- Avoid personal details like your name, birthday, username, or anything that can be guessed or found online, including the word PEX
Equally important, don’t use the same password for PEX that you use elsewhere. Whenever there’s a breach, usernames, and passwords turn up on the dark web. The password is essentially worthless outside the breached site if it isn’t used somewhere else. Best practice is still to use a password manager to generate unique strong passwords for multiple sites and keep track of them. You also want to change your passwords frequently.
2. Enable Multi-Factor Authentication
Multi-Factor Authentication (MFA) can protect your PEX account from criminals who have somehow stolen your password. Whenever anyone tries to log into your account, we send a 6-digit verification code to your phone or computer. No verification code, no access to your account.
With MFA, account access requires two totally different kinds of verification: something you know (your password) and something you have (your computer or phone). Making your account that much harder to crack. Here’s how to set up MFA for your account.
3. Watch Out for Scams and Phishing
In phishing attacks, you receive an urgent email that may look like it’s from your bank or financial services provider, and it may send you to a site that looks just like theirs. But it is, in fact, an attempt to steal your password. Always check the email address of the sender, not just the name displayed. If it’s not from a PEX card domain, forward it to our security department. Don’t click on the link. If you think there might be a legitimate concern, log into your account through the PEX mobile app or our regular website: htpps://dashboard.pexcard.com.
4. Keep Your Devices Up to Date
You know the drill. You’re in the middle of a project, on a deadline, and suddenly you get a notification that your software or device needs updating. You may be tempted to put it off until later and maybe, like many people, you forget about it. But every time you neglect an update you put your business at risk.
Most of these updates include patches for newly discovered security vulnerabilities. If security workers found it, there’s a chance criminals and hackers are on to it, too. An unpatched device can give a criminal access to all your saved account details, including logins and passwords. They may also be able to even inject malicious software into your computer to track keystrokes.
When you keep your devices up to date, you protect all your accounts. Not just PEX.
5. Remove Unused Browser Plugins and Keep the Rest Up to Date
Ad blockers. Password managers. Shopping assistants. As much as these little tools play a key role in our online experience, they can also create security risks. Every plugin is a route into your system that a criminal can try to exploit. And like any software, new vulnerabilities are always coming to light. Old browser plugins are especially vulnerable.
Be sure you only download plugins from reputable sources and check the permissions. A lot of plugins collect more data than they need. And that’s data that a criminal can get if they hack into the vendor’s system. Get those unused plugins off your system and make sure the rest are up to date.
6. Disable International PEX Transactions If You Don’t Need Them
A significant percentage of card fraud involves charges made outside the United States. When you disable international transactions, you eliminate a huge source of fraud. You’ll also receive an alert every time someone tries to use a card internationally, which can alert you if any PEX Visa card you distributed has been compromised. Here’s how to disable (and enable) international use of PEX cards.
7. Set Policies for PEX Cardholder Transactions
Unlike corporate cards that only let you set spending limits, the PEX platform gives you an enormous amount of control over when and how cards can be used. Limitations can include:
- Time-based spend limits
- Day of the week spend limits
- International and US state restrictions
- Card-not-present use
- Merchant categories
Once you set these controls, no cardholder can spend outside those rules without an administrator’s okay. If someone tries to break the rules, the system will decline the transaction and send your administrator an alert. This not only helps secure your account, but it also enforces your rules. Here’s how to set spend rules for a card.
8. Monitor Card Use
PEX gives you enormous visibility into cardholder spending. The system reports transactions in real-time, so you can spot suspicious spending more quickly and, if necessary, disable cards immediately. These reports are always up to date.
It’s also a good practice to require cardholders to use the PEX mobile app to photograph receipts and submit transaction details, including comments and accounting codes. It helps you monitor card usage better, even as it simplifies bookkeeping.
9. Defund and Terminate Unused Cards
In some companies, there’s a tendency to stockpile cards that are no longer in use. These unused cards add complexity to the management of your account, creating opportunities for errors and misuse.
If a card is not being used, defund it (if prepaid) or cut off its credit line (if it’s used in our charge card program). That way, you can be sure the funds are freed up for cards and programs that need them. Should the card data turn up in a breach, criminals won’t be able to use it. And if a card has outlived its usefulness—maybe the cardholder has moved on or the associated project has been completed—terminate it. In addition to simplifying management and minimizing opportunities for mistakes, you may save money on fees.
10. Make Sure Your Contact Information is Up to Date
Accurate contact information is one of the fundamental keys to account security. It ensures that you receive real-time alerts to unusual activity in your account or potential fraud. And that you receive important updates about changes to policies, terms, new products or product capabilities, and more.
Accurate contact information is also necessary to recover your account should you forget your password or need to change an authentication number. Keeping your credentials up to date helps you keep your account secure.
11. Give Each Administrator Only the Privileges They Need
Administrator privileges have to strike a balance between operational efficiency and security. Yes, it may be super efficient to give every administrator the ability to issue cards or request an ACH transfer to your PEX account, but it wouldn’t be secure. Even if you have 100% trust in your employees, you create opportunities for expensive mistakes and security breaches.
Best practice is to define roles for every member of your team and restrict administrative privileges to those role-based functions. In one organization, entry level bookkeepers may be able to view card usage and change transaction notes, while only a more senior person can issue and fund cards. Roles-based privileges also make each financial professional’s activities more accountable and transparent. Here’s how to set permissions for your PEX administrators.
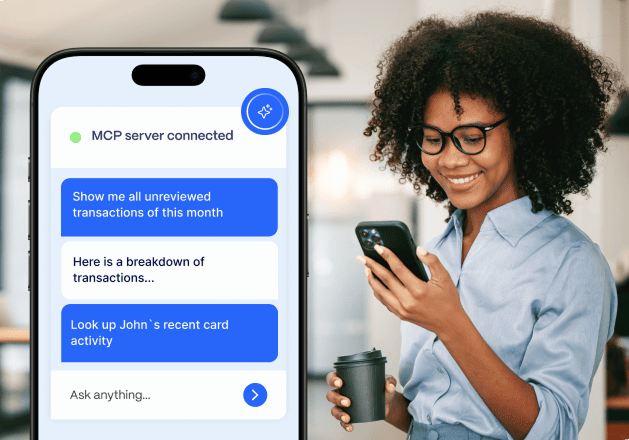
12. Download the PEX Mobile Apps for IOS and Android
PEX Mobile Apps make account security and management available to you 24 hours a day, 7 days a week. The administrator apps have the functionality of the PEX website. So you can manage your account even on the go. You also receive security alerts in real time.
The app also lets cardholders submit receipts, check their balances, and request card funding for purchases. All through a secure, auditable, cloud-based platform connected to the mobile app.
Because modern smartphones are equipped with biometric (fingerprint and facial recognition) authentication methods, mobile apps are hard to break through. PEX Mobile apps are available in the App Store for IOS and Google Play for Android.
Similar resources
Opinions, advice, services, or other information or content expressed or contributed here by customers, users, or others, are those of the respective author(s) or contributor(s) and do not necessarily state or reflect those of The Bancorp Bank, N.A. (“Bank”). Bank is not responsible for the accuracy of any content provided by author(s) or contributor(s).